Purpose of this post
The purpose of this post is to show you how we can use Azure Key Vault to secure secrets of a webapp and call them from Azure DevOps using Variable groups. This is one of the ways to handle secrets for your deployments. One of the other ways is to use Managed Identities which is more secure. I’ll cover that in a different blog post.
What are secrets and why is secret management important?
Secrets management is the process of securely and efficiently managing the safe usage of credentials by authorized application. In a way, secrets management can be seen as an enhanced version of password management. While the scope of managed credentials is larger, the goal is the same — to protect critical assets from unauthorized access.
For managing sensitive application configuration like DB connection strings, API Keys and other types of application related sensitive keys. It is recommended to use Azure Key Vault or any other secret management solution for storing secrets. Azure Key Vault is a cloud service for securely storing and accessing secrets like connection strings, account keys, or the passwords for PFX (private key files). Azure Key vault can be used for all commonly used services like Azure Webapp, Azure Kubernetes, Azure Virtual Machines and many other Azure Services.
Data like connection strings, API tokens, Client ID, Password are considered as sensitive information and handling them poorly may not only lead into security incidents but also my compromise your entire system.
Here are a couple of poorly handled secret management practices.
- Maintaining secrets in source code repository in a settings or environment config file
- Having same password/keys for all the environments
- Secrets are shared across all the team members
- Teams using service accounts to connect to the database or a server
Avoiding the above would be the first step for an effective secret management.
Using Azure KeyVault for App Services
Using Azure DevOps, All the sensitive data like Connection Strings, Secrets, API Keys, and any other data you categorize as sensitive. These values can be fetched directly from Azure Key Vault, instead of configuring them on pipeline.
Let’s take an example of configuring DB Connection string for an Azure WebApp using Azure KeyVault.
Lets create a KeyVault along with a secret in it. Notice that the key value is secret.

Similarly, lets create one more for UAT DB connection. Once created, it will show the keys created as in below screenshot.

Now in Azure DevOps, create a new variable group under the library section of pipelines.

- Give variable group a name
- Make sure to select the options “Allow access to all pipelines”, “Link secrets from Azure KeyVault”.
- Choose KeyVault name and authorize.
- Click on “Add” and select secrets for using them in the pipeline.
Below is the screenshot for reference.

Once done, in the pipeline, go to variables section click on ‘Variable groups’ and click on ‘Link variable group’ to choose the variable group that is created.
In the stages, select the environments and click link option.

Now the next step is to configure the task for applying the DB connection string to the app service.
Add and configure “Azure App Service Settings” task and in the connection strings settings, configure the JSON value for applying DB Connection string. The value here is $(Dev-DBConnectionString) that is stored in Azure KeyVault. It is picked up by the pipeline during the execution.
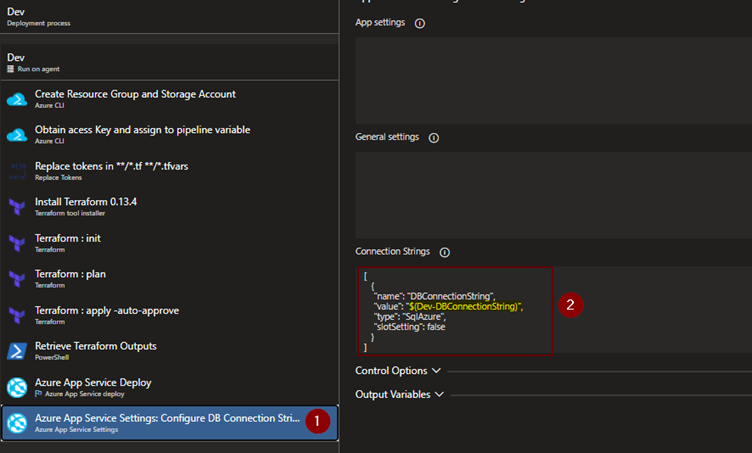
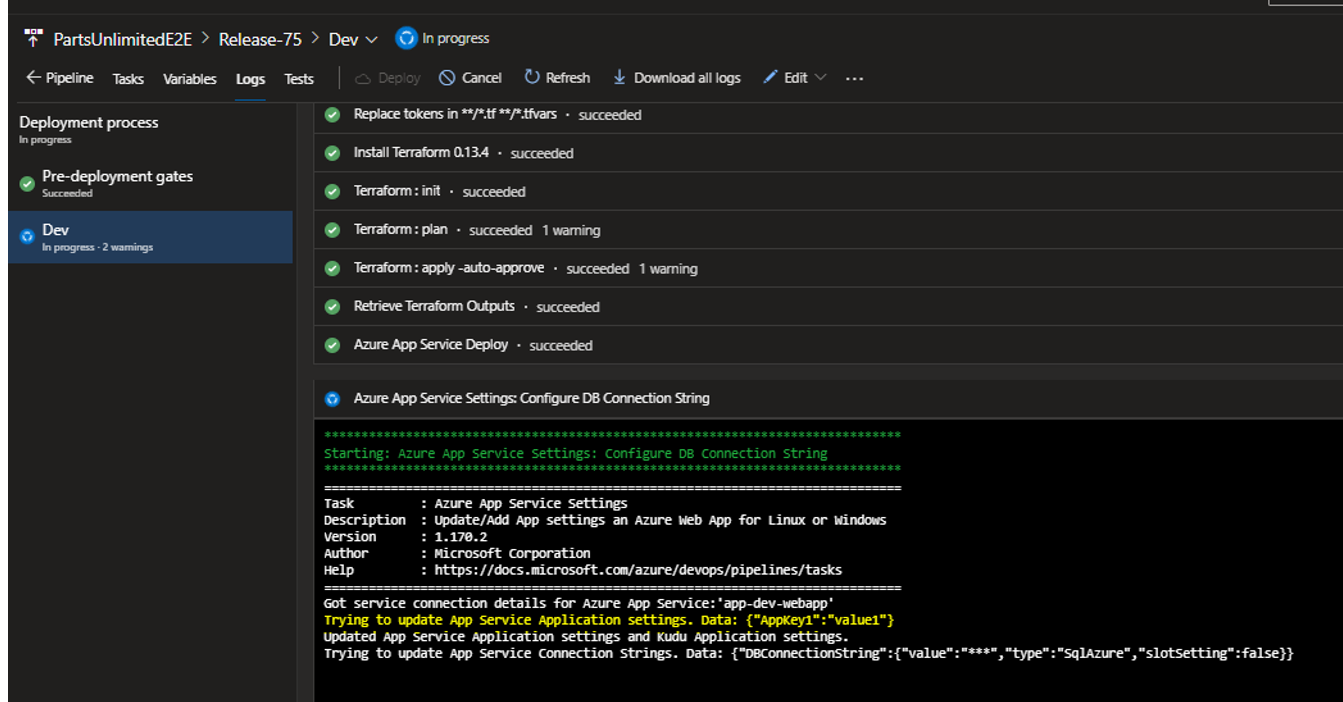
Below are the logs of the execution for the pipeline. Here it shows that the pipeline is able to fetch the value and it being a sensitive parameter, value of DB connection string is hidden in the logs.

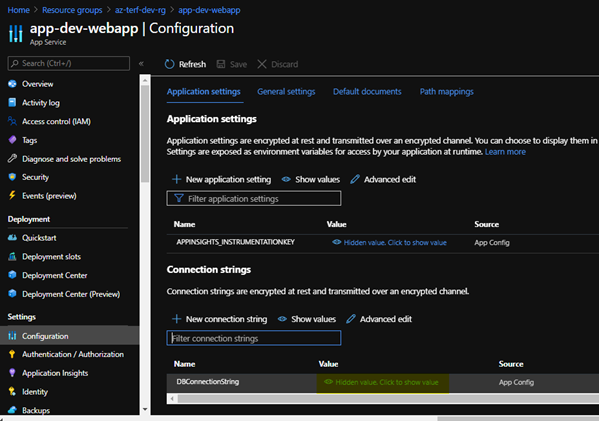
In the webapp, under configuration->Database connection strings, we will be able to see the actual value.

Once we click on the ‘show values’ we can see the value of connection string.
For configuring the other application settings which are NON-SENSITIVE, we can use ‘App Settings’ Section of “Azure App Service Settings” task to configure application settings, similar to DB Connection strings, we can use the values from key vault as well.

During the execution, we can see that application key that is configured in the above setting.
The other way to manage secrets without key vault is to use variable and the padlock option to lock the key value as shown in the below screenshots.


This way the secret is not visible to anyone, but if you would like to know the value, you need to other ways to handle it, the suggested approach is to implement a solution like Azure Key Vault with right access polices.
This brings us to the end of this blog post and we have seen how to use Azure Key Vault for Azure Web Apps with Azure DevOps and various options available to handle secrets in Azure DevOps using Variable groups and Variables.
Hope you enjoyed reading it. Happy Learning!!